Tech
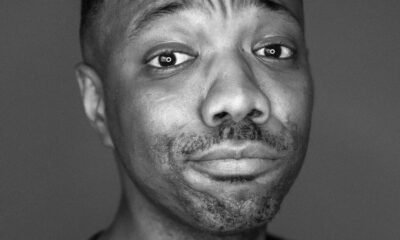
Baby X: Have We Gone Too Far?
In the rapidly evolving world of artificial intelligence, one project stands out for its uncanny ability to bridge the gap between human and machine: Baby X. This digital infant, created by Dr. Mark Sagar and his team at the University of Auckland’s Laboratory for Animate Technologies, is pushing the boundaries of what we thought possible in AI and human-computer interaction.
What is Baby X?
Baby X is a computer-generated simulation of a human infant, complete with a lifelike face and a complex AI “brain” that mimics human neural networks. Unlike traditional AI systems, Baby X is designed to learn and develop in ways that closely resemble human cognitive development.
How Does Baby X Work?
At its core, Baby X utilizes a combination of advanced computer graphics and artificial neural networks. The system is programmed with basic biological and psychological models, allowing it to:
1. Express a range of emotions through facial expressions
2. Respond to visual and auditory stimuli
3. Learn and adapt based on interactions
4. Develop rudimentary language skills
The Significance of Baby X
Advancing AI Research
Baby X represents a significant leap forward in creating AI systems that can learn and develop more naturally. By mimicking human infant cognition, researchers hope to unlock new insights into machine learning and artificial general intelligence.
Understanding Human Development
The project offers a unique platform for studying early human development. Psychologists and neuroscientists can use Baby X to test theories about infant learning and cognition in ways that would be impossible or unethical with real infants.
Improving Human-AI Interaction
As AI becomes more prevalent in our daily lives, creating systems that can interact more naturally with humans is crucial. Baby X’s ability to express emotions and respond to social cues could pave the way for more intuitive and empathetic AI interfaces.
Ethical Considerations and Future Implications
While Baby X presents exciting possibilities, it also raises important ethical questions. As AI systems become more lifelike and emotionally engaging, we must consider the psychological impact of human-AI relationships, especially on children who may not fully understand the nature of these digital entities.
Looking ahead, the technologies developed through Baby X could have far-reaching applications in fields such as:
- Education: Creating more engaging and adaptive learning systems
- Healthcare: Developing empathetic AI assistants for patient care
- Robotics: Designing more naturalistic humanoid robots
As we continue to explore the frontiers of AI, projects like Baby X remind us of both the incredible potential and the profound responsibilities that come with creating increasingly human-like artificial intelligence.
Stay Connected
Unlock impactful advertising opportunities with Bolanle Media. Our expert team crafts immersive experiences that captivate audiences, driving brand engagement and memorability. Let’s elevate your brand’s marketing strategy together.
News
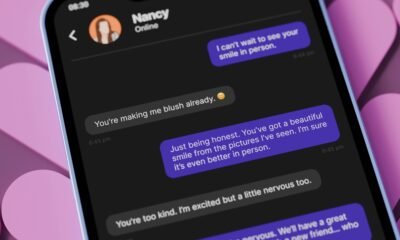
ON MAY 8, 2026, YOUR INSTAGRAM DMS STOP BEING TRULY PRIVATE
Bolanle Tech Newsroom Report
Instagram Is Quietly Changing What “Private” Means in Your DMs

From the Bolanle Tech Newsroom: Instagram has officially confirmed it will stop supporting end‑to‑end encrypted DMs on that date, and this is a documented policy change, not a rumor. That optional encrypted mode was the one feature that kept certain chats locked so tightly that not even Meta could read them, and once it’s gone, your “private” conversations lose their highest level of protection. In simple terms, the lock on those messages is being removed, and Meta will once again be in a position to see more of what you say in DMs if it chooses to, or if it is compelled to by law.
End‑to‑end encryption is what made some Instagram chats feel like a sealed envelope: the message left your phone scrambled and only arrived readable on the other person’s device. Without that, your DMs sit on Meta’s servers in a form that can be scanned by safety systems, reviewed for policy violations, and potentially used to inform AI and ad targeting. Meta is presenting this as a clean‑up of a “low‑usage” feature and is directing privacy‑focused users toward WhatsApp instead. But if you’ve been sending addresses, money talk, contracts, intimate photos, or receipts over Instagram, this marks a serious shift in what “private” really means on the platform.
“THESE CHATS WON’T BE PUBLIC, BUT THEY WON’T BE FULLY LOCKED DOWN EITHER.”
Practically, this does not mean your DMs become public or searchable by other users—strangers still can’t just open your messages, and your audience settings, blocking, and reporting tools remain in place.

What changes is who else can see inside: Meta’s internal systems, safety tools, and, when required, law enforcement will have a clearer path to the content of your conversations than they did under full end‑to‑end encryption. That is why privacy advocates are sounding the alarm—and why, from the Bolanle Tech Newsroom, our guidance is to treat Instagram DMs as semi‑public space: useful for networking, coordination, and light conversation, but not the place to keep your most sensitive secrets.
Entertainment
The machine isn’t coming. It’s aleady the room.

The machine isn’t coming. It’s already in the room.
Picture this: you spend two years writing a script. You hustle funding, build a team, reach out to casting. Then somewhere inside a studio, a software platform analyzes your concept against fifteen years of box office data and decides—before a single human executive reads page one—that your film is too risky to greenlight.
This isn’t a Black Mirror episode. This is Hollywood in 2026.
The Numbers Don’t Lie
The generative AI market inside media and entertainment just crossed $2.24 billion and is projected to hit $21.2 billion by 2035—a 25% annual growth rate. Studios like Warner Bros. are running platforms like Cinelytic, a decision-intelligence tool that predicts box office performance with 94–96% accuracy before a single dollar of production money moves.
Netflix estimates its AI recommendation engine saves the company $1 billion per year just in subscriber retention. Meanwhile, over the past three years, more than 41,000 film and TV jobs have disappeared in Los Angeles County alone.
That’s not a trend. That’s a restructuring.

The Moment That Changed Everything
In February 2026, ByteDance’s AI generator Seedance 2.0 produced a hyper-realistic deepfake video featuring the likenesses of Tom Cruise, Brad Pitt, and Leonardo DiCaprio. It went viral instantly. SAG-AFTRA called it “blatant infringement.” The Human Artistry Campaign called it “an attack on every creator in the world.”
Then came Tilly Norwood—a fully AI-generated actress created by production company Particle 6—who was seriously considered for agency representation in Hollywood. The first synthetic human to knock on that door.
Matthew McConaughey didn’t mince words at a recent industry town hall. He looked at Timothée Chalamet and said:
“It’s already here. Own yourself. Voice, likeness, et cetera. Trademark it. Whatever you gotta do, so when it comes, no one can steal you.”
James Cameron told CBS the idea of generating actors with prompts is “horrifying.” Werner Herzog called AI films “fabrications with no soul.” Guillermo del Toro said he would “rather die” than use generative AI to make a film.
But here’s the thing—not everyone agrees.
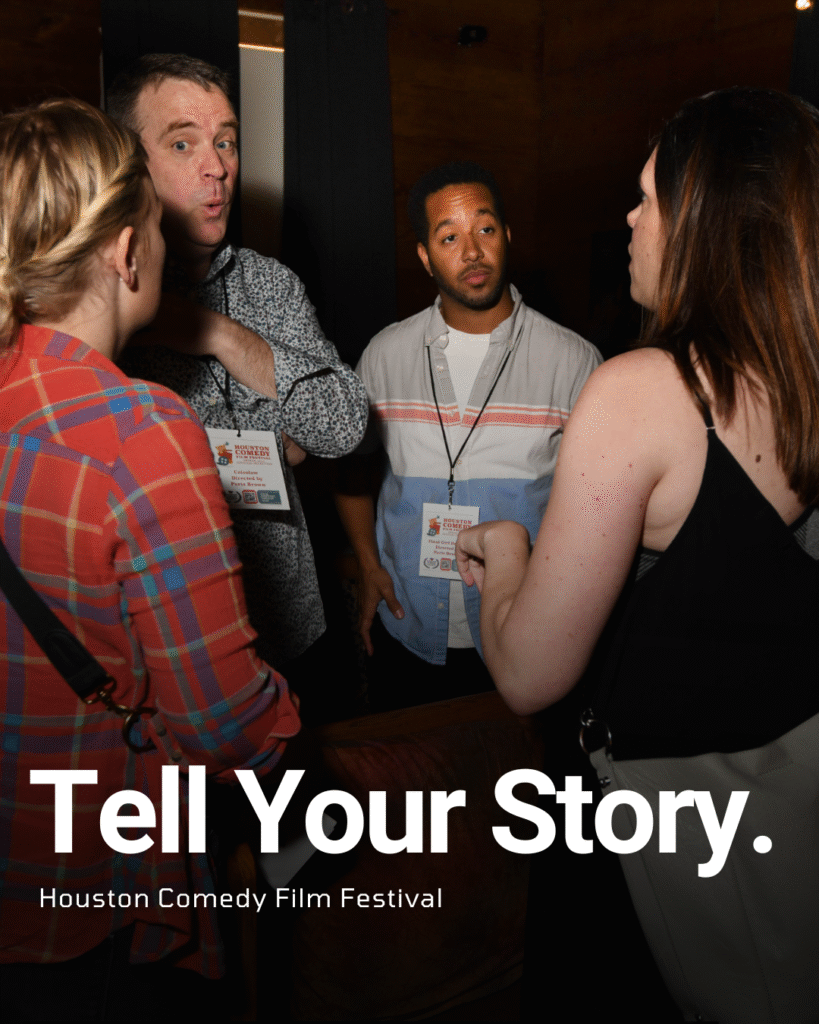
The Indie Filmmaker’s Double-Edged Sword
At SXSW 2026, indie filmmakers made something clear in a packed panel: they don’t want AI to make their movies. They want AI to “do their dishes.”
That’s the real conversation happening at the ground level.
Independent filmmaker Brad Tangonan used Google’s AI suite to create Murmuray—a deeply personal short film he says he never could have made without the tools. Not because he lacked talent, but because he lacked budget. He wrote it. He directed it. The AI executed parts of his vision he couldn’t afford to shoot.
In Austin, an independent filmmaker built a 7-minute short in three weeks using AI-generated video—a project that would have taken 3–4 months and cost ten times more the traditional way. That’s the version of this story studios don’t want you focused on.
At CES 2026, Arcana Labs announced the first fully AI-generated short film to receive a SAG-approved contract—a milestone that proves AI-assisted production can operate inside union protections when done right.
The Fight Coming This Summer
The WGA contract expires May 1, 2026. SAG-AFTRA’s expires June 30. AI is the headline issue at the bargaining table—and the last time these two unions went to war with studios over it, Hollywood shut down for 118 days.
SAG is expected to push the “Tilly Tax”—a fee studios pay every time they use a synthetic actor—directly inspired by Tilly Norwood’s emergence. The WGA already prohibits studios from handing writers AI-generated scripts for a rewrite fee. Now they want bigger walls.
Meanwhile, the Television Academy’s 2026 Emmy rules now include explicit AI language: human creative contribution must remain the “core” of any submission. AI assistance is allowed—but the Academy reserves the right to investigate how it was used.
The Oscars and Emmys are essentially saying: the robot didn’t get nominated. The human did.
What This Means for You
If you’re an indie filmmaker between 25 and 45, you’re operating in the most disruptive creative environment since the camera went digital. AI can cut your post-production time by up to 40%. It can help you pre-visualize shots, generate temp scores, clean up audio, and pitch your project with a sizzle reel you couldn’t afford six months ago.
But the machine that helps you make your film is the same machine that could make studios decide they don’t need you to make theirs.
Producer and director Taylor Nixon-Smith said it best: “Entertainment, once a sacred space, now feels like it’s in a state of purgatory.”
The question isn’t whether AI belongs in your workflow. It’s whether you’re the one holding the wheel—or whether the wheel is slowly being handed to an algorithm that has never once felt what it means to have a story only you can tell.
Business
Harvard Grads Jobless? How AI & Ghost Jobs Broke Hiring

America’s job market is facing an unprecedented crisis—and nowhere is this more painfully obvious than at Harvard, the world’s gold standard for elite education. A stunning 25% of Harvard’s MBA class of 2025 remains unemployed months after graduation, the highest rate recorded in university history. The Ivy League dream has become a harsh wakeup call, and it’s sending shockwaves across the professional landscape.
Jobless at the Top: Why Graduates Can’t Find Work
For decades, a Harvard diploma was considered a golden ticket. Now, graduates send out hundreds of résumés, often from their parents’ homes, only to get ghosted or auto-rejected by machines. Only 30% of all 2025 graduates nationally have found full-time work in their field, and nearly half feel unprepared for the workforce. “Go to college, get a good job“—that promise is slipping away, even for the smartest and most driven.
Tech’s Iron Grip: ATS and AI Gatekeepers
Applicant tracking systems (ATS) and AI algorithms have become ruthless gatekeepers. If a résumé doesn’t perfectly match the keywords or formatting demanded by the bots, it never reaches human eyes. The age of human connection is gone—now, you’re just a data point to be sorted and discarded.
AI screening has gone beyond basic qualifications. New tools “read” for inferred personality and tone, rejecting candidates for reasons they never see. Worse, up to half of online job listings may be fake—created simply to collect résumés, pad company metrics, or fulfill compliance without ever intending to fill the role.
The Experience Trap: Entry-Level Jobs Require Years
It’s not just Harvard grads who are hurting. Entry-level roles demand years of experience, unpaid internships, and portfolios that resemble a seasoned professional, not a fresh graduate. A bachelor’s degree, once the key to entry, is now just the price of admission. Overqualified candidates compete for underpaid jobs, often just to survive.
One Harvard MBA described applying to 1,000 jobs with no results. Companies, inundated by applications, are now so selective that only those who precisely “game the system” have a shot. This has fundamentally flipped the hiring pyramid: enormous demand for experience, shrinking chances for new entrants, and a brutal gauntlet for anyone not perfectly groomed by internships and coaching.
Burnout Before Day One
The cost is more than financial—mental health and optimism are collapsing among the newest generation of workers. Many come out of elite programs and immediately end up in jobs that don’t require degrees, or take positions far below their qualifications just to pay the bills. There’s a sense of burnout before careers even begin, trapping talent in a cycle of exhaustion, frustration, and disillusionment.
Cultural Collapse: From Relationships to Algorithms
What’s really broken? The culture of hiring itself. Companies have traded trust, mentorship, and relationships for metrics, optimizations, and cost-cutting. Managers no longer hire on potential—they rely on machines, rankings, and personality tests that filter out individuality and reward those who play the algorithmic game best.
AI has automated the very entry-level work that used to build careers—research, drafting, and analysis—and erased the first rung of the professional ladder for thousands of new graduates. The result is a workforce filled with people who know how to pass tests, not necessarily solve problems or drive innovation.
The Ghost Job Phenomenon
Up to half of all listings for entry-level jobs may be “ghost jobs”—positions posted online for optics, compliance, or future needs, but never intended for real hiring. This means millions of job seekers spend hours on applications destined for digital purgatory, further fueling exhaustion and cynicism.
Not Lazy—Just Locked Out
Despite the headlines, the new class of unemployed graduates is not lazy or entitled—they are overqualified, underleveraged, and battered by a broken process. Harvard’s brand means less to AI and ATS systems than the right keyword or résumé format. Human judgment has been sidelined; individuality is filtered out.

What’s Next? Back to Human Connection
Unless companies rediscover the value of human potential, mentorship, and relationships, the job search will remain a brutal numbers game—one that even the “best and brightest” struggle to win. The current system doesn’t just hurt workers—it holds companies back from hiring bold, creative talent who don’t fit perfect digital boxes.
Key Facts:
- 25% of Harvard MBAs unemployed, highest on record
- Only 30% of 2025 grads nationwide have jobs in their field
- Nearly half of grads feel unprepared for real work
- Up to 50% of entry-level listings are “ghost jobs”
- AI and ATS have replaced human judgment at most companies
If you’ve felt this struggle—or see it happening around you—share your story in the comments. And make sure to subscribe for more deep dives on the reality of today’s economy and job market.
This is not just a Harvard problem. It’s a sign that America’s job engine is running on empty, and it’s time to reboot—before another generation is locked out.

 Advice2 weeks ago
Advice2 weeks agoHow to Make Your Indie Film Pay Off Without Losing Half to Distributors

 Advice2 weeks ago
Advice2 weeks agoHow to Find Your Voice as a Filmmaker

 Business4 weeks ago
Business4 weeks agoWhat the Michael Biopic Means for Every Indie Filmmaker

 Business3 weeks ago
Business3 weeks agoGLOBAL SUSTAINABILITY SUMMIT RETURNS FOR ITS 5TH EDITION AT THE BRITISH PARLIAMENT – HOUSE OF LORDS, PALACE OF WESTMINSTER

 News2 weeks ago
News2 weeks agoCan AI Really Steal Your Fingerprints From a Selfie?

 Film Industry2 weeks ago
Film Industry2 weeks agoActors Win AI Deal – But Your Face Is Still Training the Machine

 Entertainment2 weeks ago
Entertainment2 weeks agoOzempic Era: Beauty, Lizard Venom, Big Pharma

 Business2 weeks ago
Business2 weeks agoBuilding a 10 Million Army: One Leader’s Mission to Save Tomorrow